Rising concerns about embedded security
Embedded systems are becoming ubiquitous. Due to trends such as the Internet of Things (IoT) and machine-to-machine communication (M2M) the number of connected devices and machines are increasing. Many of these – from small household appliances through large communication networks to complex, industrial automation systems – are controlled by special-purpose, embedded computing systems.
While this networking trend continues to gather pace – promising greater convenience and comfort for users and new business and service models for companies – security in this embedded world often lags far behind. Security vulnerabilities are rising dramatically as the attack surface widens and manufacturers struggle to protect sensitive data, IP and process integrity.
Meeting today’s security challenges with OPTIGATM
Our OPTIGATM family of security solutions is designed for easy integration into embedded systems. These hardware-based security
solutions scale from basic authentication functionality to advanced implementations meeting your individual and changing needs, while maximizing the return on your investment. Both our OPTIGATM Trust and OPTIGATM TPM product families provide proven and reliable embedded security performance.
OPTIGATM Trust E | OPTIGATM Trust P
Ease of integration paired with tailored authentication performance
Our OPTIGATM Trust family of turnkey, programmable solutions gives you the benefit of easy and convenient integration whilst offering you the most suitable security level to protect your business model, process know-how and IP. You can rely on OPTIGATM Trust products to protect your embedded systems against counterfeiting, unauthorized products, intentional attacks and unintentional operator errors.
Basic authentication solution for your embedded application
OPTIGATM Trust (SLS 10ERE) is a robust cryptographic solution for embedded systems requiring easy-to-integrate authentication features. It is designed to assist system and device manufacturers in proving the authenticity, integrity and safety of their original products. As a turnkey solution, it provides enhanced protection against aftermarket counterfeit replacements and helps to maintain OEM authenticity.
Key features
- Advanced cryptographic algorithm implemented in hardware (ECC163)
- Turnkey solution including host-side software for easy integration
- 5 kbit user memory
- Unique asymmetric key pair per chip
- Size-optimized PG-USON-3 package (2 x 3 mm)
Key benefits
- Lower system costs due to single-chip solution
- Increased security with asymmetric cryptography and chip-individual keys
- Easy integration thanks to full turnkey design
Applications
- IoT edge devices
- Printer cartridges
- Consumer accessories
- Original replacement parts
- Medical & diagnostic supply equipment
OPTIGATM Trust E
Easy, cost-effective security solution for high-value goods
OPTIGATM Trust E is a high-end turnkey security controller with full system integration support for easy and cost-effective deployment. It supports a broad range of uses cases focused on the protection of services, business models and user experience. One-way authentication mechanisms uniquely identify objects and protect PKI networks.
Key features
- High-end security controller with an advanced cryptographic algorithm implemented in hardware (ECC256)
- Turnkey solution with OS, Applet and complete host-side integration support
- I2C interface and PG-USON-10 package (3 x 3 mm)
- Up to 3 Kbytes user memory
- Standard & extended temperature range -40° to +85°C
- Compliant to USB Type-C standard
Key benefits
- Reduced design-in and integration effort
- Protection of IP and data
- Protection of business models & company image
- Safeguarding of quality and safety
Applications
- Embedded systems networked over the IOT
- Industrial control and automation
- Medical devices & Consumer electronics
- Smart homes
- PKI networks
OPTIGATM Trust P
Programmable trust anchor for embedded systems
OPTIGATM Trust P (SLJ 52ACA) is a high-security, feature-rich solution. As a fully programmable chip, it is a highly flexible and secured solution supporting the full range of functions from authentication and secured updates through key generation and access control. This hardware security microcontroller provides advanced and efficient protection against side-channel, fault-induction, and physical attacks.
Key features
- High-end security controller with advanced cryptographic algorithms implemented in hardware (ECC521, RSA2k, DES. AES)
- Common Criteria EAL 5+ (high) certification
- Programmable JavaCard operating system with reference applets for a variety of use cases and host-side support
- 150 KB user memory
- Small footprint VQFN-32 SMD package (5 x 5 mm)
Key benefits
- Secured and certified solution
- Increased flexibility based on programmable solution with reference applets to simplify customization and integration
- Protection of system integrity, communication and data
Applications
- Industrial control systems
- Energy generation and distribution systems
- Healthcare equipment and networks
- Consumer electronics
- Home security and automation
- Embedded systems networked over the IOT
Certified security solutions for computing and emerging IoT applications
OPTIGATM TPM (Trusted Platform Module) is a standardized security controller which protects the integrity and authenticity of devices and systems in embedded networks. Built
on proven technologies and supporting TPM 1.2 and the latest TPM 2.0 standard, OPTIGATM TPM highlights include secured storage for keys, certificates and passwords as well as dedicated key management. As the established, trusted market and innovation leader in the Trusted Computing space, we offer a broad portfolio of certified OPTIGATM TPM) security controllers based on the Trusted Computing Group (TCG) standard to suit all needs.
Key features
- High-end security controller with advanced cryptographic algorithms implemented in hardware (e.g. RSA & ECC256, SHA-256)
- Common Criteria (EAL4+) and FIPS security certification
- Flexible integration with SPI, I2C and LPC interface support
- Extended temperature range (-40 to +85°C) for a variety of applications
Key benefits
- Reduced risk based on proven technology
- Fast time to market through concept reuse
- Flexibility thanks to wide range of security functions as well as dedicated key management
- Easy integration into all platform architectures and operating systems
Applications
- PC and embedded computing
- Network equipment
- Industrial control systems
- Home security and automation
- Energy generation and distribution systems
- Automotive electronics
We understand that security needs are as varied as they are complex. Scaling from basic, single-function authentication solutions to robust certified security controllers for advanced platform integrity checks, we have developed the market’s widest portfolio to support individual security needs across a broad market spectrum.
OPTIGATM TPM in networking applications
Challenge:
As an entry point to corporate, home or industrial networks, routers and gateways are especially vulnerable to outside attacks. A failure to protect these entry points can result in the loss of confidential information as well as interrupted operations.
Solution:
Equipped with an OPTIGATM TPM the network equipment enables the uninterrupted operation of the system as well as protecting sensitive information by relying on the standardized, certified OPTIGATM TPM solutions. It can do so by performing integrity checks, securely managing the equipment remotely as well as supporting the encryption of information transferred through and stored in the router or gateway. With its extensive functionality it allows to satisfy both basic security needs as well as fulfilling complex requirements as your needs evolve.
OPTIGATM Trust E in industrial applications
Challenge:
Industrial automation, medical equipment, electronic components – plagiarism of capital equipment and consumer products endangers both, user experience and safety as well as companies business models and investments. According to the OECD, counterfeiting and piracy costs add up to around 638 billion US dollars annually.
Solution:
The new OPTIGATM Trust E offers an easily implementable solution to protect manufacturers’ valuable IP from being attacked, analyzed, copied and modified. Enhanced authentication as well as secured storage of software codes and product data improve network and supply chain management – particularly in the context of Industry 4.0. And help manufacturers of high value goods to safeguard their IP and protect their brand through assured quality and safety of their products.
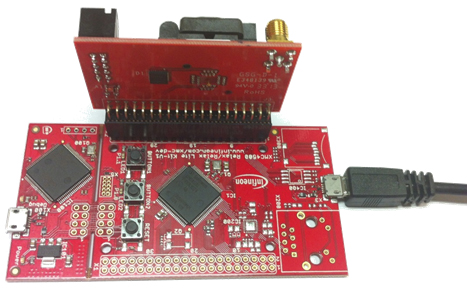
Evaluation Boards
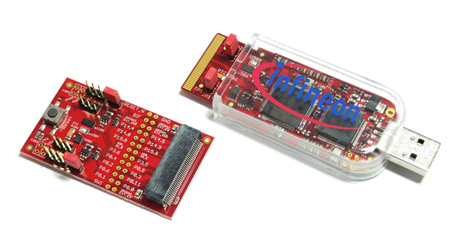
OPTIGATM Trust
Get started with the OPTIGATM Trust with the demo kit. The kit includes a host MCU and an OPTIGA™ Trust SLS10ERE. It has a JTAG interface as well as an I/O Extension Card with an additional SLS10ERE. The demo kit comes with a user manual, and a graphical user interface for evaluation purposes. It also includes a Dave IDE as well as a HiTop Debugger. All in all a this is a full scale demo kit to get you started.
OPTIGATM Trust P
Learn more about the OPTIGATM Trust P with the demo kit. It gets you started by demonstrating the functionalities of the OPTIGATM Trust P and is expandable to a full development kit with a software download from an Infineon Secure Site. The kit includes both the host controller board as well as connection cables, demo utility software (for the PC) and a demo system user guide.
OPTIGA™ TPM SLB 9645 IRIDIUM

Get started for your embedded system with the OPTIGATM TPM evaluation board today. The IRIDIUM plug-in board can be used to evaluate the OPTIGATMTPM for both a Raspberry Pi and Beagle Board. It comes with an extensive application note enhanced by the publicly available Linux setup and drivers, software stacks and so on. Everything you need to get started with TPM for your application is available – start securing your application today.
For further use cases, there are also Xenon evaluation boards available for all of the OPTIGATM TPM products that allow you to easily test and evaluate the TPM functionalities.
Join our webinar and discover the benefits of dedicated hardware-based security
Embedded devices are increasingly connected and as part of this connectivity increasingly at risk to be manipulated or attacked. Attackers can gain access to valuable information such as IP and customer data or can manipulate the system or even introduce counterfeit devices. To prevent this, strong embedded security measures are needed. Attendees will learn the fundamentals of how embedded systems are at risk and what can be done to protect them.
Key Take-Aways
- Learn the fundamentals of how embedded systems in Internet-of-things or industrial applications can be secured
- Understand the benefits of dedicated hardware security in your system
- Find out which type of security functions you need to protect your system and supply chain
- Learn about Infineon Technologies security solutions and the OPTIGA™ family of security controllers
Watch our free of charge webinar:
Security for the IoT – Do You Know How to Secure Your Embedded System?